Cryptocurrency Transaction Security: Precautions Small Businesses Should Take

On October 11, Chainalysis published a fascinating study that highlighted Latin America as a region with a smaller crypto economy compared to other areas like East Asia and Eastern Europe. However, the region’s position has remained remarkably stable since 2021, according to the study. This analysis is backed by a Global Cryptocurrency Adoption Index, where three Latin American countries—Brazil, Argentina, and Mexico (ranked 9th, 15th, and 16th, respectively)—are among the top 20 nations in terms of cryptoasset utilization. There are also intriguing findings, such as 92.5% of crypto volume in Venezuela being channeled through centralized services. Additionally, Mexico, one of the world’s largest recipients of international remittances (estimated at around 61 billion dollars per year), received 5.4% of this market in 2022 through a major cryptocurrency firm.
Why focus on Latin America? In regions plagued by persistent devaluations and economic crises, individuals are driven to find ways to circumvent the limitations imposed by the system. They are motivated to think creatively about what they, as individuals, can do to secure their well-being and, in the process, fulfill the needs of our society. I’m not suggesting that change cannot originate from the government; I simply want to highlight that changes tend to be more significant and productive when initiated by individuals themselves.
With or without economic and political crises, the influence of online shopping continues to surge; it’s a phenomenon that’s firmly rooted in our society. The potential of the e-commerce industry has revolutionized our way of thinking and has captured the interest of countless entrepreneurs. In a previous post, we explored the advantages and challenges of embracing cryptocurrencies. We found that not only do digital assets complement traditional payment methods, but the challenges associated with their use are not overly complex. If you’re a business owner who has recently decided to accept crypto payments, we’d like to offer some precautions for your consideration.
The first step is to secure your money. As we mentioned in our last post, there are different types of wallets. What’s the safest option? Physical wallets or hardware wallets, small devices about the size of a keychain. These tools store the user’s private key offline. The private key is the key that grants access to your funds, and this is where the popular phrase “not your keys, not your coins” comes from, which you’ve probably heard or seen before.

Many people underestimate this concept. In companies like Binance or Coinbase, users are not the guardians of their funds, even though they rightfully own them. If the exchange closes due to regulatory pressure or declares bankruptcy, our only recourse is to await the completion of legal procedures and trials to recover some of our money. A well-known example is the case of Mt. Gox, once one of the largest cryptocurrency exchanges, handling over 70% of global crypto transactions at its peak. It began in 2010 and declared bankruptcy in February 2014. This not only caused Bitcoin’s value to plummet by nearly half in a month but also resulted in a staggering debt of 850,000 bitcoins (equivalent to $29.43 billion at the time of writing this article).
You may have your reasons for storing funds on an exchange like Binance, but one critical mistake you should avoid is keeping a substantial amount of money on centralized services and expecting it to remain secure indefinitely. While digital wallets like Electrum, Coinomi, or Exodus can be used (which has its advantages since the user retains ownership of their private keys), it’s essential to note that they can be susceptible to hacking. An illustrative example is the incident involving the Webaverse project, where co-founder Ahad Shams confirmed in early 2023 that approximately $4 million was stolen from his Trust Wallet. Shams thinks that the hacking occurred during a meeting, and he wasn’t connected to a public Wi-Fi network, so he believes the thieves only needed a photograph of the wallet screen displaying the balance.
Setting up a Digital Wallet
Let’s dive into a practical example to guide you through the process of configuring a digital wallet. In this demonstration, we’ll use Exodus on an Android device running version 13, as well as the desktop version for Windows.
1. Download Exodus Wallet: Begin by visiting the Play Store or App Store to download the Exodus wallet. In our case, as we’re using an Android device, head to the Play Store. After installing the application, click on the “Create a Wallet” option.
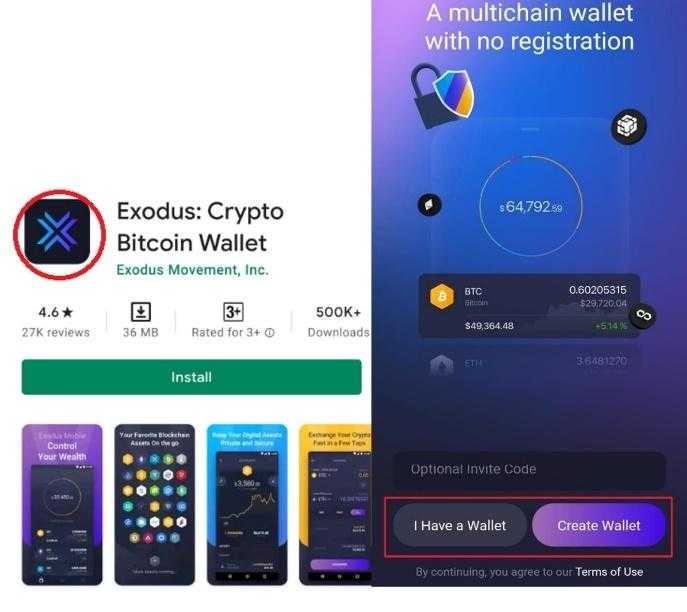
After selecting “Create Wallet,” you’ll be presented with your “seed phrase” — a sequence of words essential for accessing the wallet. Given that logging out directly within the application isn’t possible (you’d need to navigate to Settings > Google > Applications > Exodus > Delete Data), we highly recommend promptly activating the security PIN. This ensures that every time you exit the application on your smartphone, it will prompt you for a 6-digit code upon re-entry.
2. Activate the security PIN: Go to the Main Menu > Security > Secure with Passcode.
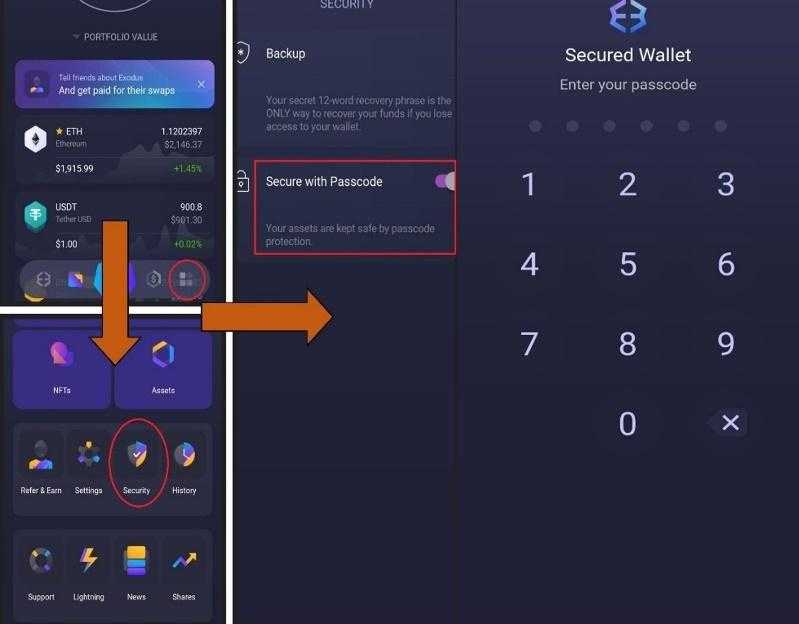
Now that we have activated our unlock PIN, let’s explore how to manage your portfolio, focusing on sending and receiving money. In order to receive funds into your wallet or transfer cryptocurrency from another service to Exodus, you’ll need to locate the “Deposit Address”.
3. Finding the deposit address: Navigate to your portfolio, select the desired cryptocurrency, and click on the downward arrow symbolizing incoming transactions. Let’s use BTC as an example.
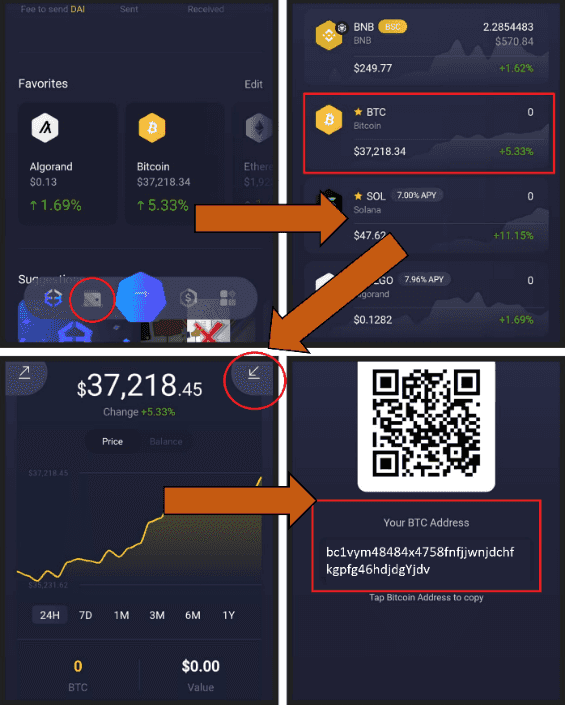
In this way, we can find our deposit addresses, which we’ll need to enter into other wallets or services when initiating a withdrawal to Exodus. Now, let’s proceed to withdraw money from Exodus. Achieving this reversal involves locating the deposit address of the receiving wallet, where the funds will be directed.
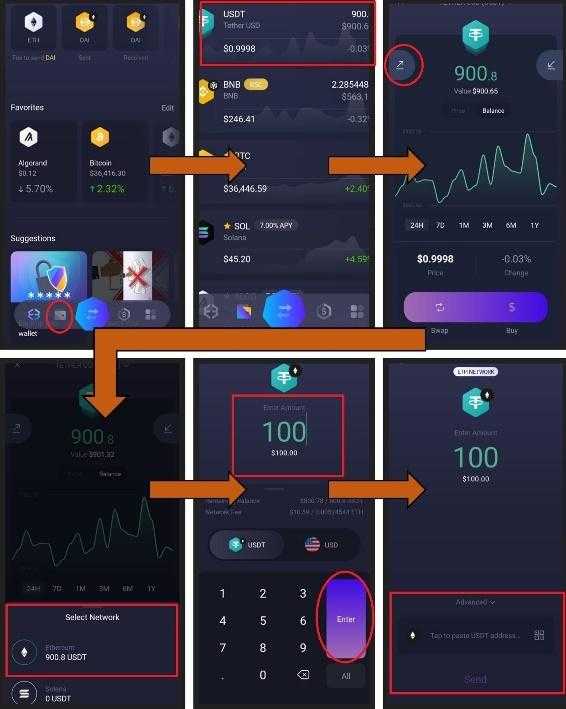
4. Withdraw money from Exodus: Go to the portfolio, click on the balance you want to withdraw, then tap the upward-facing arrow, indicating outgoing transactions. Finally, select the network through which the transaction will be conducted. In this example, we’ll use USDT and the Ethereum network (ERC-20). Enter the withdrawal amount, press Enter, and paste the address where the funds will be received.
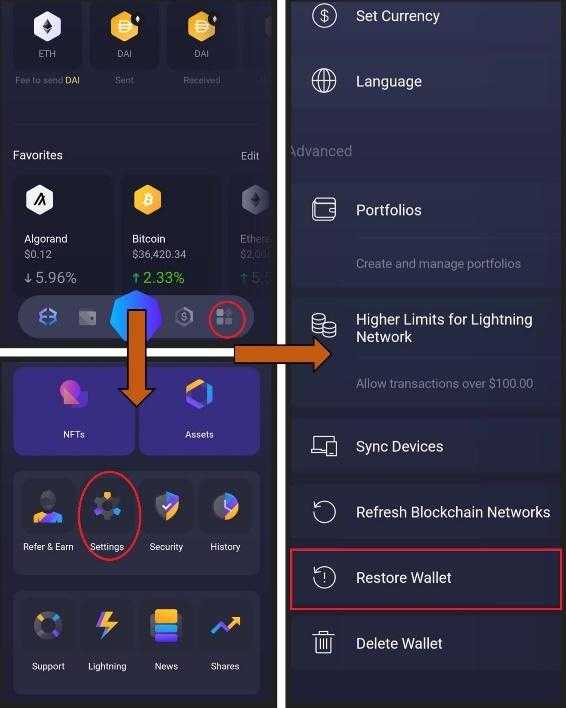
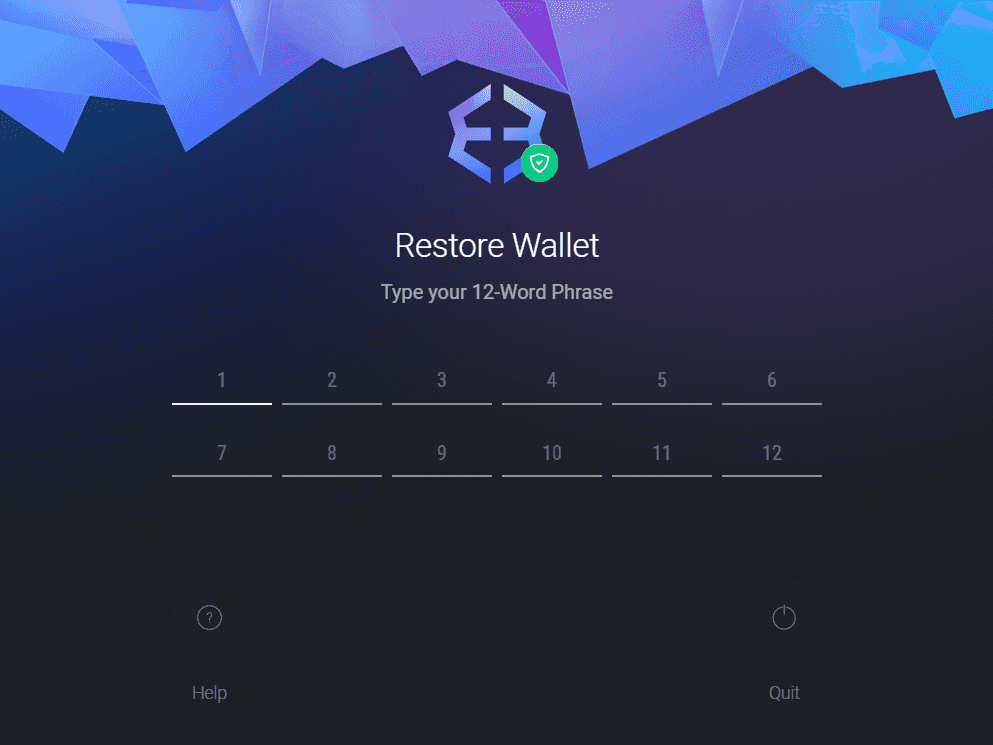
5. Restore our wallet: If our smartphone is stolen or lost, we can recover our wallet by downloading the application, selecting “I Have a Wallet” (refer to illustration 1), and entering our 12 keywords. Alternatively, we can restore our wallet by clicking Main Menu > Settings > Restore Wallet.
6. Cryptocurrency swap: If we wish to exchange our tokens for other crypto assets, a service facilitated by third-party providers, simply press the button with bidirectional arrows. Choose the asset you want to exchange, select the token you expect to receive, and specify the amounts. Just below, you can view the rate and the network fee.

If you lose your seed phrase but still have access to the wallet because you never logged out, there’s a way to recover your 12 keywords. Simply go to the Main Menu, click on Security, then select Backup, and finally, choose “View Secret Phrase”. Afterward, enter the unlock PIN, and the app will guide you to a section where you only need to use the “Press and Hold to Reveal” button.

Next, we will guide you through the basic configuration of the desktop version of Exodus.
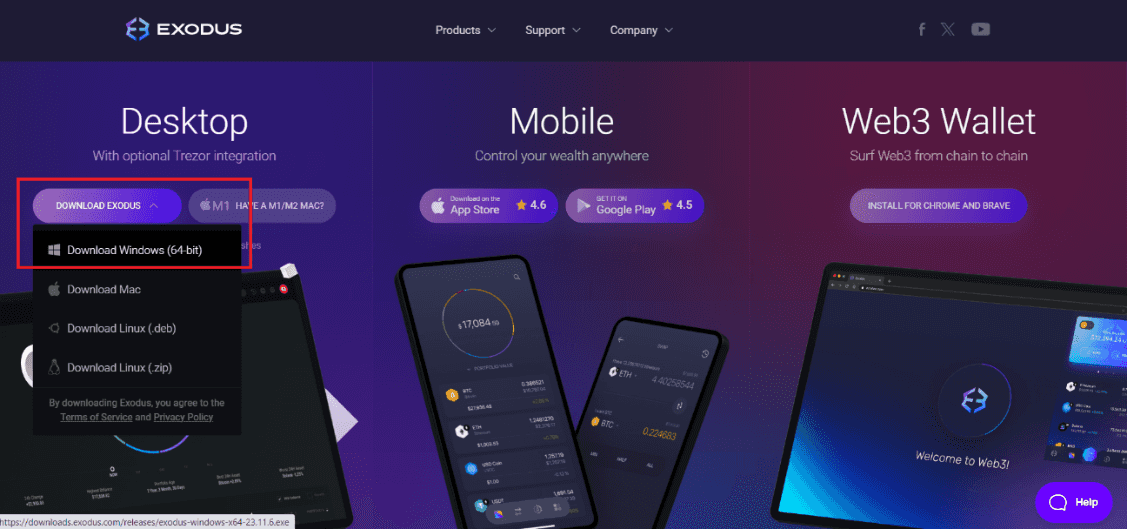
1. Download the program: Visit the official product page and download the application. We did it using Google Chrome.
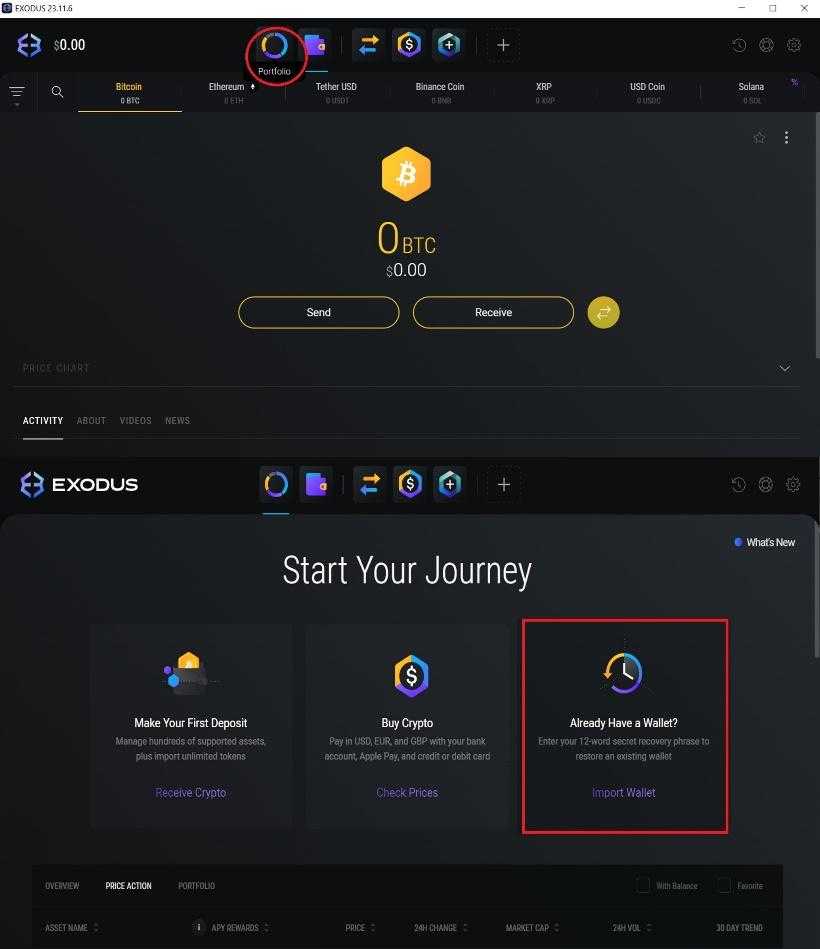
2. Import the wallet: Click on the Portfolio section, and then select Import Wallet. The program will prompt a restart, and afterward, you’ll need to enter your 12 keywords. Click Restart and enter your seed phrase.
2.1. However, there’s a way to synchronize devices and directly access our funds. Click on Settings > Devices > Sync Devices > Sync to Device. This also applies to the mobile app.
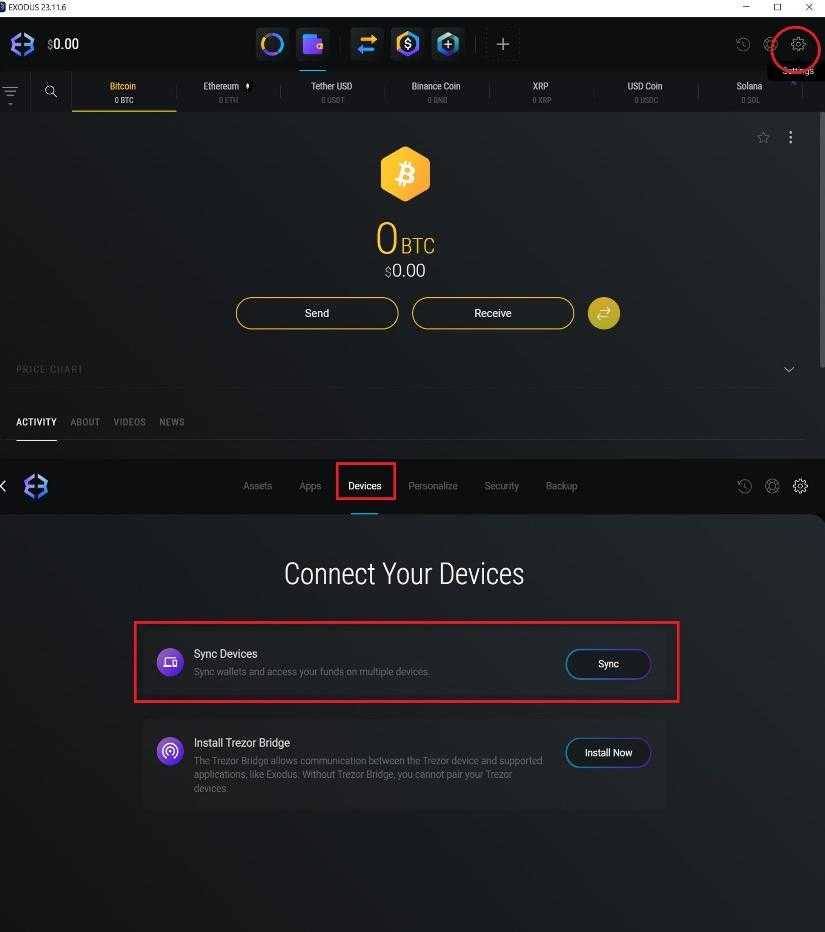
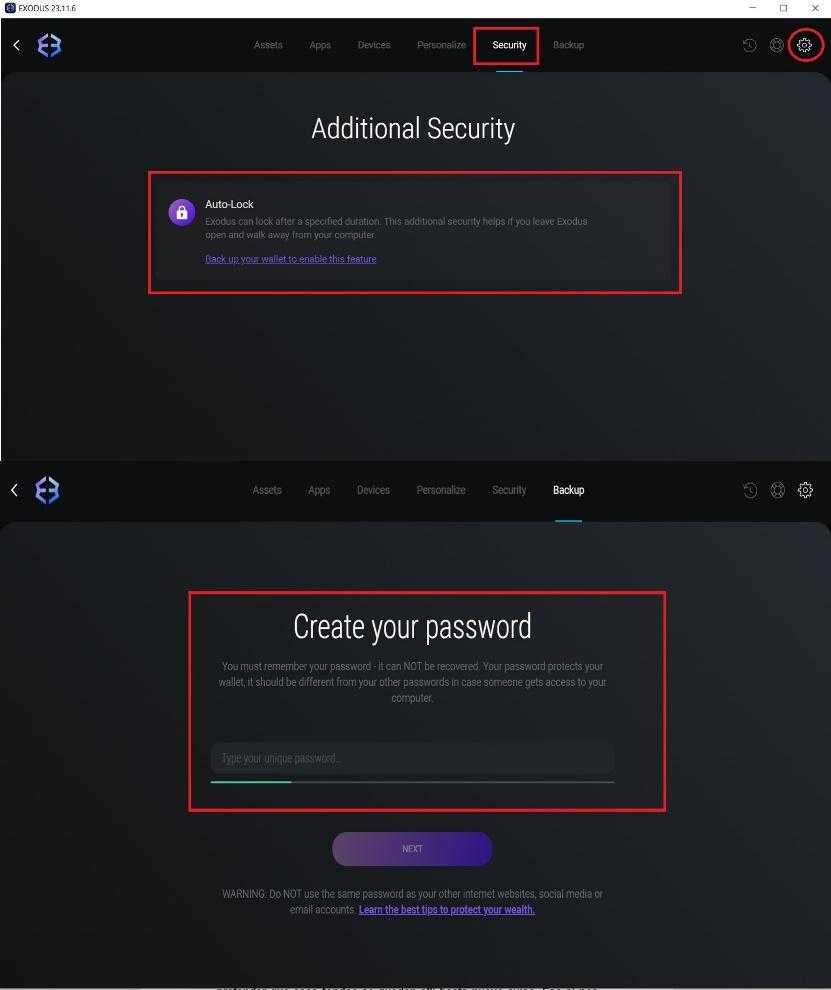
3. Lock function: Similar to the mobile version, there’s a function that lets us add an extra layer of security, ensuring the application locks whenever we close it. Access this function by clicking on Settings > Security > Autolock. The final step is to set up an unlock PIN.
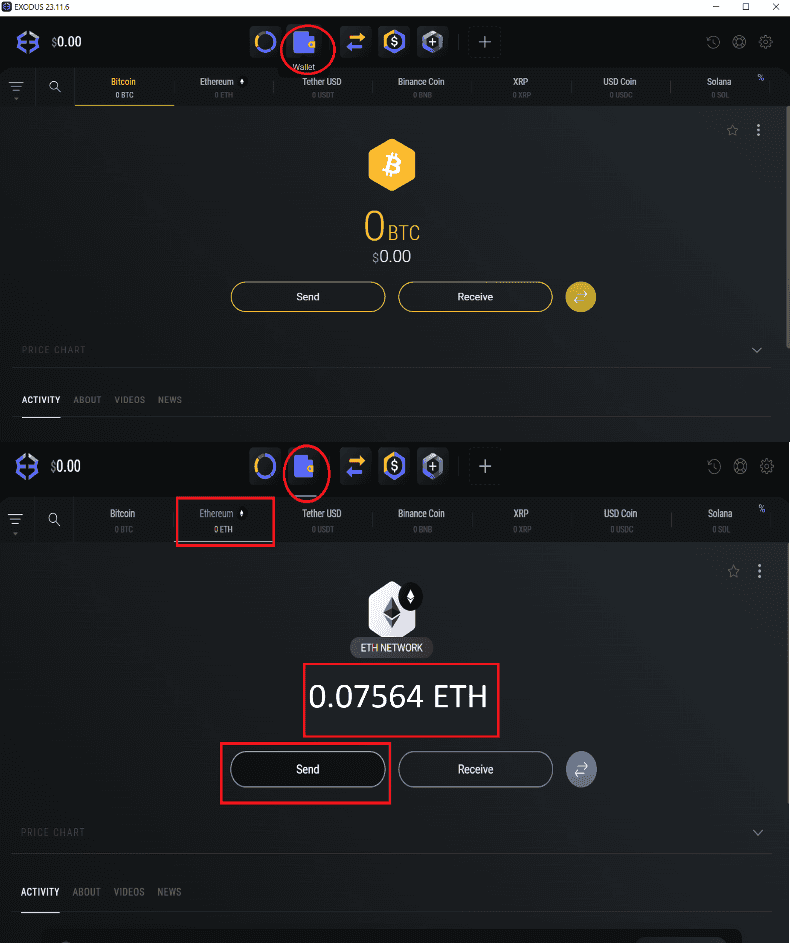
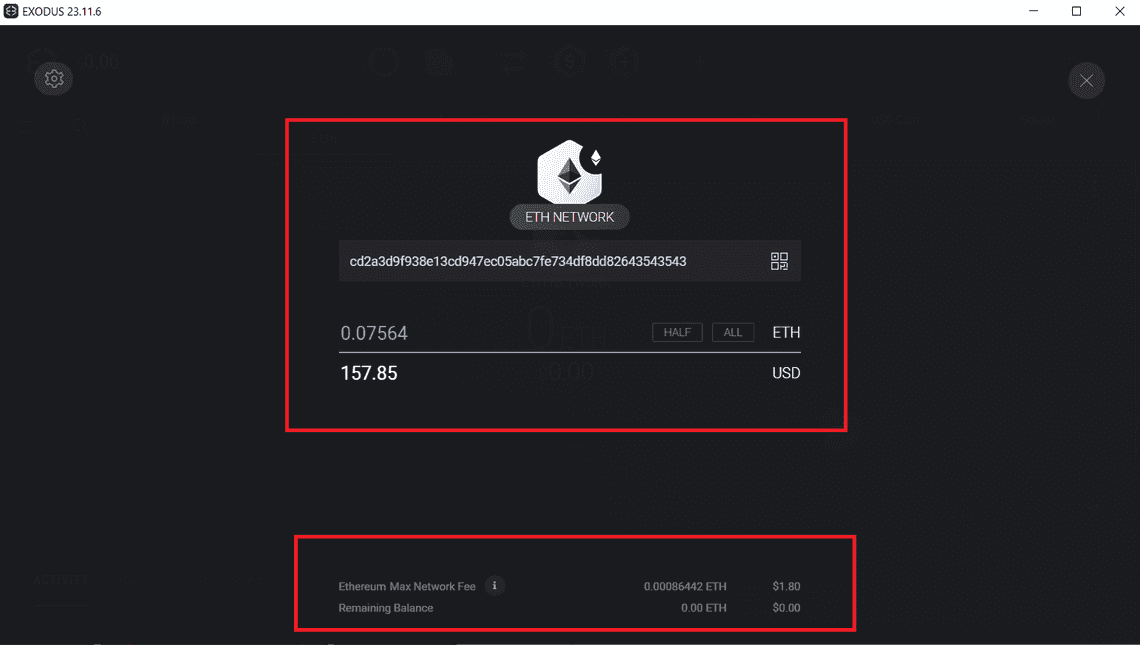
4. Withdraw/Send: Navigate to the Wallet section, choose the crypto asset of interest, and click on Send. Paste the address that will receive the funds and specify the amount you want to send.
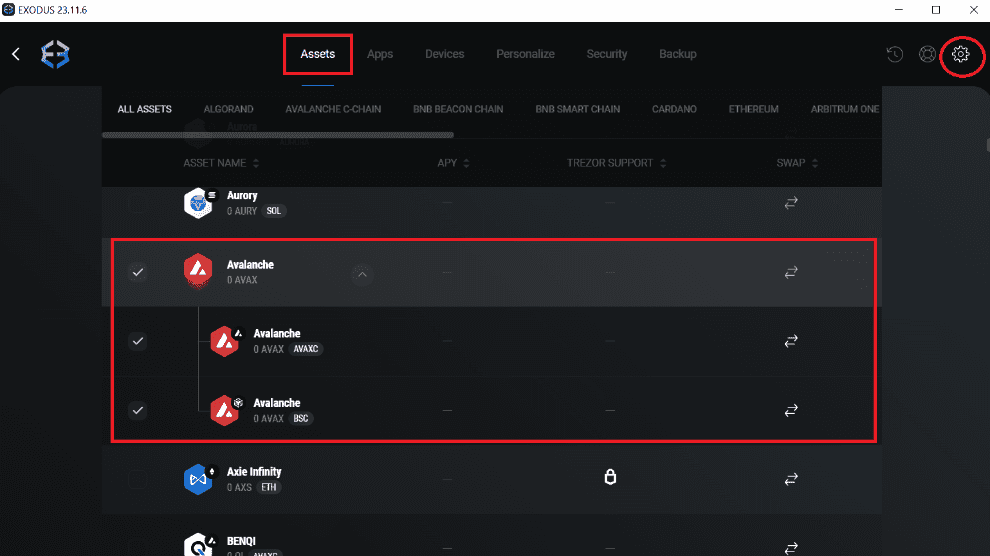
It should be noted that we can search for specific crypto assets, enabling or disabling their visibility in our panel. This can be done by navigating to Settings > Assets.
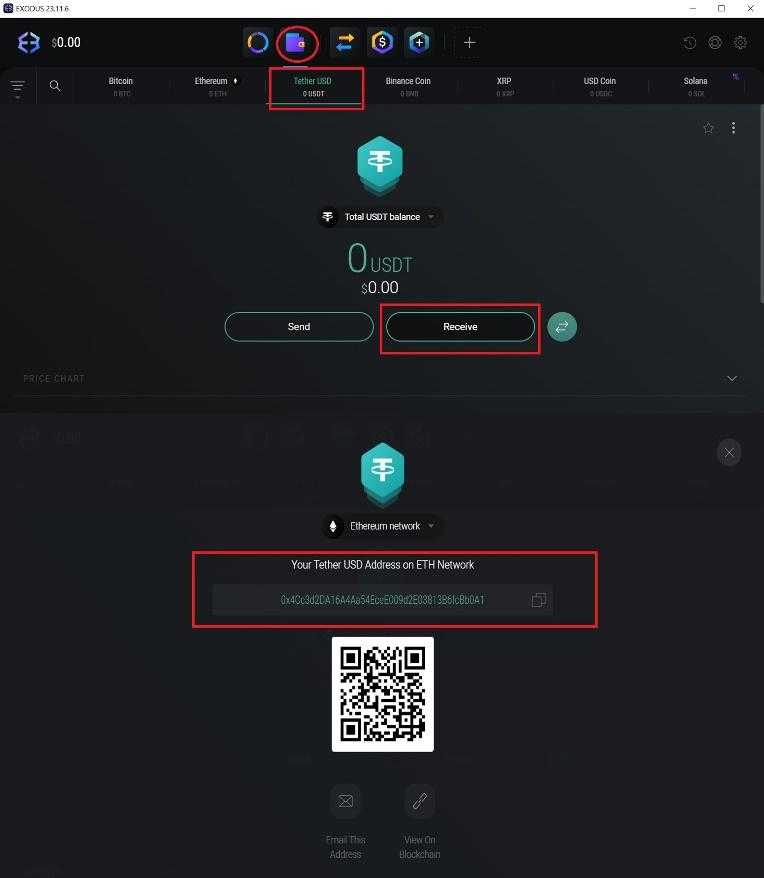
5. Deposit/receive funds: The process is as straightforward as in the case of the mobile app. Navigate to Wallet, choose the asset you want to receive, click on Receive, and you’ll be presented with your deposit address. Alternatively, you can scan a QR code from the device sending the funds.
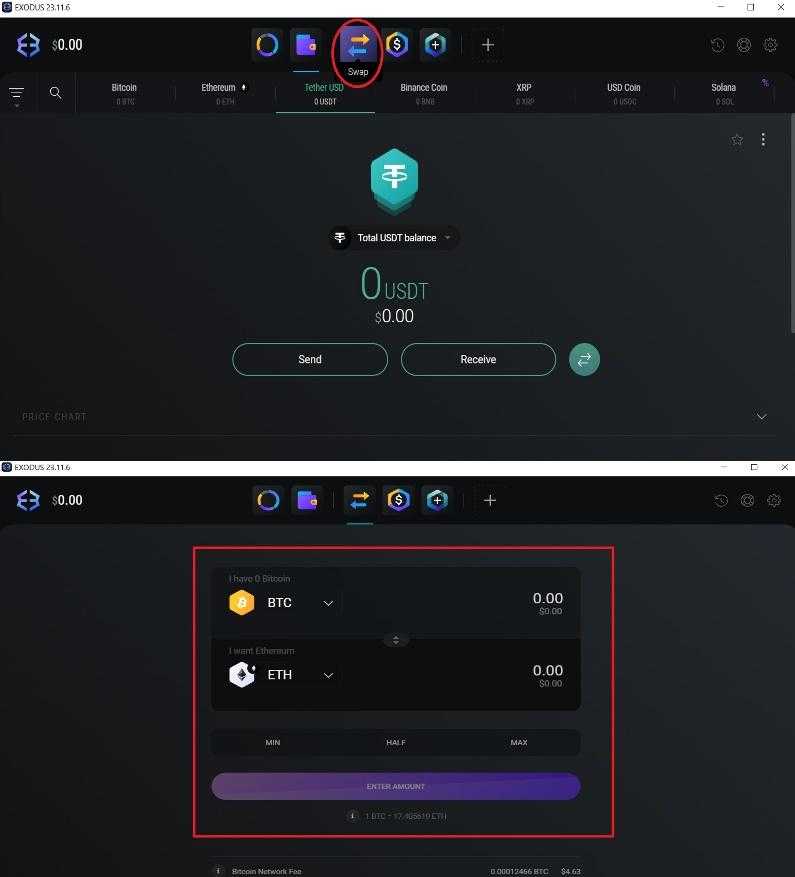
6. Cryptocurrency swap: It uses the same icon as the mobile app. Below, you can view the rates and the network fee.
Exodus Wallet doesn’t feature a logout button, a characteristic shared by both the mobile app and the desktop version. But fear not, logging out of the PC version is as simple as clicking on the standard X used to close any application. This action prevents unauthorized access to the program. When you wish to re-enter, a Welcome Back window will appear, prompting you to enter the password configured in step number 3.
While some argue that achieving 100% security with any method is impossible, we firmly believe that physical wallets significantly reduce the risk. We’re not suggesting that digital wallets are a condemned choice; in fact, we consider them essential, especially for those new to the world of crypto assets. The smart approach is diversification—avoiding the practice of depositing substantial sums in one location and expecting them to remain untouched indefinitely. This strategy, in our view, would be a mistake.

Additional recommendations:
- If you find it necessary to utilize a centralized exchange for strategic or business reasons, it’s essential to choose the right platform and avoid depositing your money just anywhere. Always remember to conduct thorough research and opt for well-established, reputable platforms.
- Staying informed about the happenings in the crypto world is crucial. Knowledge is power. Cryptocurrency markets can be sensitive to global events, and the value of cryptocurrencies can fluctuate quickly. We suggest making use of stablecoins.
- Avoid being lured by trends in the crypto industry and refrain from investing a portion of your profits in any crypto venture impulsively.
- Be sure to write down the private keys of your wallets. Storing such sensitive information on a computer is not advisable. You can keep this information in a physical notebook and create multiple backups. Be cautious of hiding places that might be vulnerable to fires or floods.
- If you plan to purchase a physical wallet, ensure that you acquire it from authorized distributors and avoid purchasing from third-party sellers who may offer counterfeit devices. Beware of scammers producing fraudulent hardware wallets.
Providing more options always brings extra value and a competitive edge. Consumers greatly appreciate simplifying their lives, so embracing cryptoassets is just the first step to reaching a wider audience. However, we must exercise caution and consider multiple aspects. While it’s impossible to cover everything in a single article, we can highlight key points for your knowledge and ongoing learning. The crypto world offers benefits and technological solutions that would have seemed impossible 20 years ago, but it also requires guidance and, most importantly, responsibility. We’re here to assist and make your journey as smooth as possible.
Decentralization and strong security measures are crucial in today’s world. These principles have guided our development of the protocol we’re diligently working on. Embracing decentralization, LOAD adds an extra level of security, mitigating exposure to occasional hacks that may impact third-party-guarded services. By integrating the most secure storage options, such as physical and digital wallets, with our proactive business model for LOAD, where buyers and sellers are not only rewarded in tokens but also actively participate in the governance of the platform while conducting transactions in various cryptocurrencies, users can shape a robust security strategy to protect their assets.
Quick Links
Legal Stuff
Social Media
